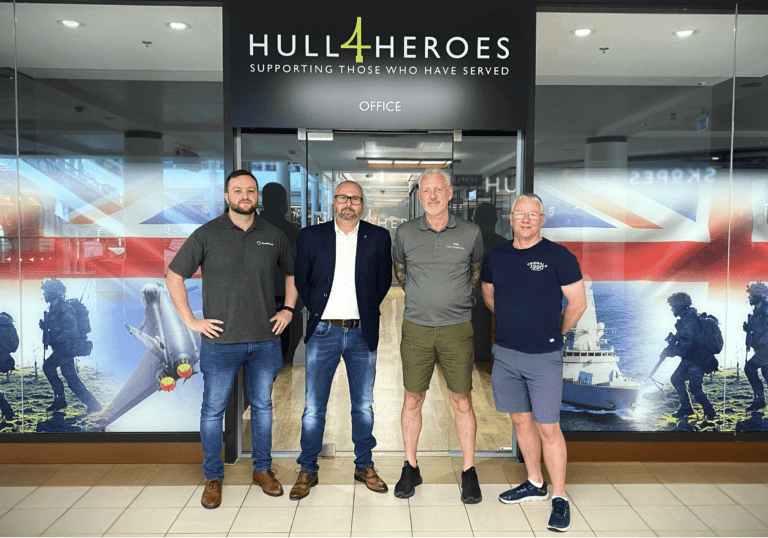
Hull IT Company Lends Its Support to Local Charity
Hull-based charity, Hull 4 Heroes, transform their internal processes with SharePoint implementation, thanks to support from local IT company HBP Syst...
Appointment of Head of People at HBP Systems
IT and software provider, HBP Systems, has introduced a wave of new employee benefits following the appointment of new Head of People, Sarah Sutherlan...
HBP Awarded Accreditation From Best Companies
We're delighted that The HBP Group has been awarded One Star accreditation from Best Companies, highlighting us as a very good company to work for in ...
The Yorkshire Three Peaks Challenge 2022
Following from our completion of The Yorkshire Three Peaks Challenge in 2019 our team once again tackled one of the toughtest endurance tests around o...
HBP Nominated For Two Northern Lincolnshire Business Awards
We are delighted to announce that we have been nominated for two awards at the upcoming Northern Lincolnshire Business Awards.
Introducing the Tech How and Tech Fix teams
We are delighted to announce the launch of our new Tech How team, and the re-naming of the servicedesk to the Tech Fix team.
Lebus Upholstery and HBP Systems
Scunthorpe based furniture manufacturers, Lebus Upholstery, have made a significant investment in their internal IT systems in order to increase staff...
HBP Systems 30 Years in Business
On November 1st 2021 we officially celebrate our 30th anniversaries for HBP Systems. Although the future of the business is always at the forefront of...

